Argentum IT LLC Blog
One of the reasons that information technology keeps changing is for the sake of the user and their convenience using it. However, if this convenience comes at the sacrifice of your business’ cybersecurity, it just isn’t worth it. This is the crux of why we always recommend that any organization seeking to use password management should invest in a reputable password management software, rather than the built-in capabilities of modern browsers.
With so many threats in business, it doesn’t take much to fall victim to a cyberattack or a scam. Understanding the dangers out there is the first step in enacting a cybersecurity process that can keep your users and your business safe. Let’s take a look at how to build one in this month’s newsletter.
Ransomware is one of the worst situations that any business could have to deal with. It not only holds your data or computing infrastructure for ransom, it also creates situations where you have to explain to your clientele that you’ve been breached and that their information has fallen into the hands of scammers looking to extort your business. This month, we thought we would take you through a ransomware attack to give you an idea of just how unpleasant it is.
Cyberattacks are a serious problem that all businesses face in some form or another, but there are small, everyday tasks you can do to ensure that they impact your organization as minimally as possible. It takes intention and effort to protect your business and its infrastructure, but that doesn’t mean that it has to be hard. Here are three simple ways you can keep your infrastructure secure.
The increase in wearable technology that you see coming into your business has substantially increased over the past couple of years. People are doing a better job of tracking their health and using wearable technology to improve their work lives. This creates a problem for the business because every single device brought onto a network is a potential threat and threats have to be managed. Let’s take a look at how people are using wearable technology and what you can do in response to this trend.
So much goes into proper network security that it can be daunting to know where to start. Thankfully, there are plenty of great ways you can, and probably currently are, protecting your business, even if it’s on a basic level. You can consider this a checklist of crucial network security tools that are important to have for your company’s success.
Phishing attacks have consistently been prominent in cybercrime throughout the past few years, not only due to their efficacy but also because there are so many avenues wherein phishing can be attempted. The first that comes to mind is email, of course, but you and your team need to keep these others in mind.
Take, for instance, a phishing voicemail…dubbed, naturally, a “phoicemail.”
Email remains a cornerstone in business communications, often containing sensitive information and other data that really needs to be protected. Fortunately, modern email platforms often enable you to add a little bit of protection, so long as you know what the process looks like.
Let’s go over how you can make your emails just that much more secure.
Regardless of your industry, there are going to be certain regulatory standards that you will be responsible for upholding. Many of these standards will be related in some way to your cybersecurity. Let’s talk about some of these cybersecurity standards, and why compliance is so critical for your business.
The blockchain has been a hot topic in the past few years, if only tangentially. With all the buzz around cryptocurrencies, it can be easy to forget about the underlying technology that powers it and its other applications. Let’s pivot to these other applications for a moment and discuss how the blockchain could potentially be involved with security needs at some point in the future.
The modern threat landscape is vast and unpredictable, and even if you think you know enough about cybersecurity to protect your business, we bet that you don’t. It’s not even just in the business world, either; individuals also struggle against cyberthreats, and so too do IT administrators. The next couple of weeks will be dedicated to cybersecurity to get across everything you need to know about it.
For a long time, businesses that didn’t have any cybersecurity problems would never consider investing in additional cybersecurity tools. The decision-makers of these companies simply didn’t find it necessary; and many of them had a point (until they didn’t). Today’s threat landscape is much, much more complex than it was only a few short years ago and therefore businesses need to make a point to set up the security tools that will help them secure their network and infrastructure from threats. Let’s take a look at some strategies that work to help modern businesses secure their digital resources:
While many small businesses shrug off cybersecurity needs as too expensive an investment for an organization of their size, this is a potentially catastrophic mistake. The fact of the matter is that small businesses are regularly targeted by cyberattacks, making the aforementioned cybersecurity needs even more needed.
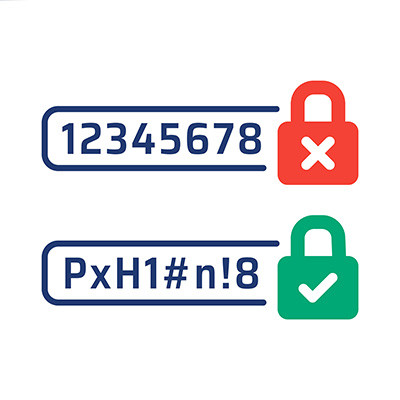
Simple passwords are often the bane of a business’ existence. If you routinely use strings like Password, 123456, Guest, or Qwerty to secure an account, then you need to reexamine your password practices before they lead to a data breach. A good password can go a long way toward helping you in this effort.
We get it—nobody likes to think about the prospect of being impacted by a cybersecurity incident, but it’s like any other unpleasant event in that it is best to prepare for it. In fact, today’s businesses can invest in a cyber insurance policy to help prepare for such an eventuality.
Let’s go over some of the ins and outs of cyber insurance so that you are prepared to make the best choice of provider for your business.
With so many threats out in the world, it’s no surprise that some of them target undiscovered vulnerabilities. These types of threats use what are called zero-day exploits to make attempts at your sensitive data and technology infrastructure. What is it about zero-day exploits that you must keep in mind during your day-to-day operations and in planning for the future?
Let me ask you a question: how much did you pay Google for your Business Profile? Unfortunately, if the answer was anything other than “nothing,” you’ve been scammed. Google has actually announced that they are taking legal action against scammers who impersonated the company in order to defraud small businesses.